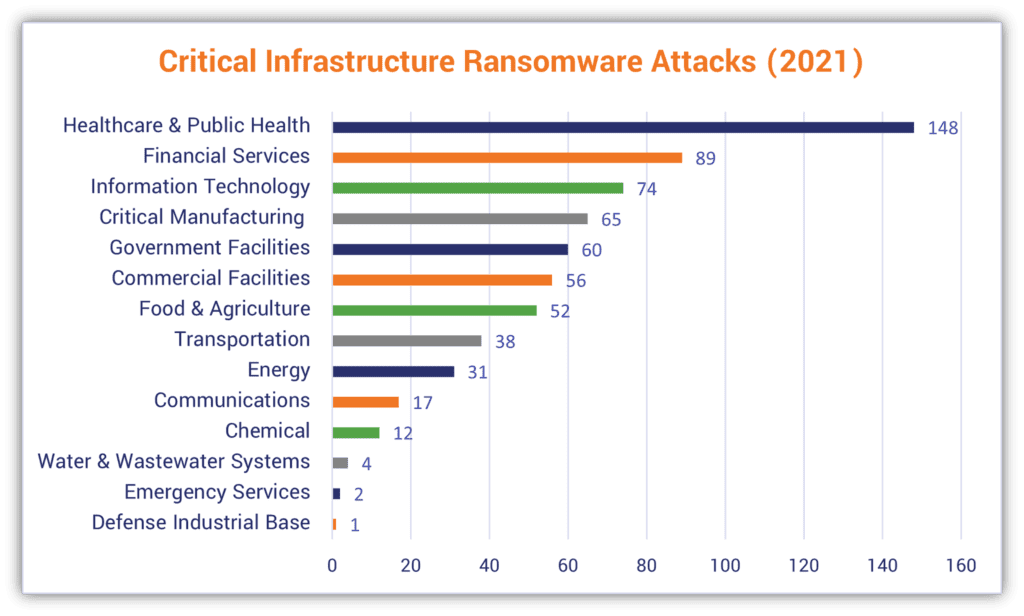
First appearing in early 2023, 8Base Ransomware caught attention when attacks surged notably throughout the summer months.
An 8Base attack becomes apparent through a ransom note confirming your systems are locked and files encrypted. These specialist criminals typically require cryptocurrency payment to maintain anonymity. Without payment, they threaten data deletion or public exposure of your information.
When discovering physical evidence of a crime at your premises, your immediate response would be to alert the authorities and secure the scene, recognising that contamination could compromise the investigation.
The same principle applies to a cyber breach. Your priority should be engaging specialist forensic professionals while keeping all systems exactly as they are.
Your internal IT personnel or managed service provider aren't equipped for this task. Round-the-clock Digital Forensic experts exist specifically to handle these situations.
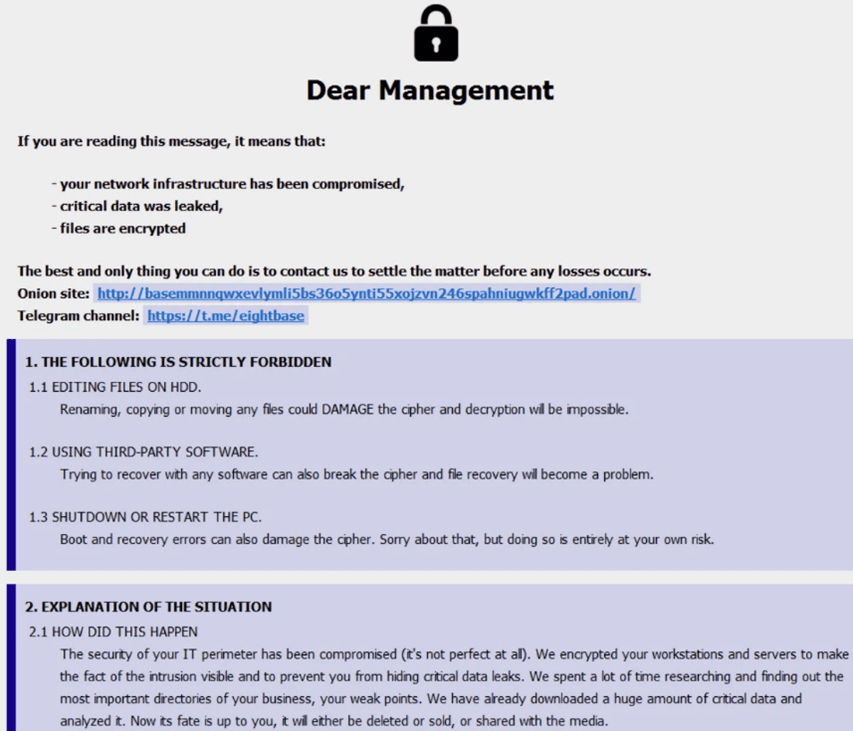
An 8Base ransomware compromise typically announces itself through a ransom message appearing on your systems.
Since May 2023, 8Base has operated using a double extortion strategy. The group maintains a TOR-based leak site where they publish victim information. Their initial access typically comes through phishing campaigns or purchasing credentials from initial access brokers.
The attackers steal sensitive data first, then deploy encryption, creating a two-pronged threat that forces victims into a difficult position. Even organisations with robust backup systems face significant risk. The stolen data creates exposure that goes beyond operational disruption, threatening both reputation and regulatory compliance. Cybercriminal groups favour this approach because it substantially improves their success rate in securing ransom payments.
8Base appeared in its present iteration during the first quarter of 2023. Security researchers have identified technical overlaps with established ransomware operations including Phobos, RansomHouse, and HIVE, leading to speculation that 8Base represents a rebrand or evolution of an earlier threat actor.
The group's victim count currently stands at 455 compromised organisations.
With round-the-clock availability every day of the year, Solace Cyber has delivered Digital Forensic Incident Response services across hundreds of successful recovery operations in Australia.
Steps After a Security Breach
When a cyber incident occurs, take these immediate actions:
Solace Cyber acts as your specialist digital forensics partner in Australia, helping restore normal operations swiftly. Our response includes:
Recovery timelines typically range from 2 weeks to 2 months, depending on the incident's scope.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
“1,957 cyber incident reports received by the NCSC Incident Management (IM) team between Sep 2023–Aug 2024. Up from 1,226 two years prior.”
When a cyber incident occurs, take these immediate actions:
Solace Cyber acts as your specialist digital forensics partner in Australia, helping restore normal operations swiftly. Our response includes:
Recovery timelines typically range from 2 weeks to 2 months, depending on the incident's scope.
Solace Cyber delivers global risk and security services across Australia, specialising in travel, crisis support, and offshore risk management. The organisation runs a fully staffed security operations centre around the clock and maintains an internal intelligence unit that produces routine daily and weekly updates. The business is certified to ISO 27001, ISO 14001, ISO 45001, and ISO 9001 standards.
Founded in the UK in 2021, Solace Cyber has grown its presence throughout Australia, concentrating on cyber incident handling, including digital forensics, incident response, ransomware events, information security, and wider risk management, supported by managed security services. The senior leadership team has more than two decades of combined experience across security and IT.
s
%+
Specialist forensic investigation and secure restoration demand focused expertise that standard IT departments rarely possess. Your internal teams excel at day-to-day technology support, but ransomware response requires dedicated capabilities they typically lack.
Consider these key challenges facing in-house teams:


We created Solace Cyber specifically to address ransomware incidents through our structured 6-phase methodology:
Our comprehensive forensic investigation begins at phase 2, forming the foundation of your business continuity plan. This detailed analysis proves essential for:
We execute our evidence examination according to a carefully structured protocol designed to identify root causes quickly. This discovery directly informs our eradication strategy and recovery plan, while building the evidence base for potential legal action. Through legal proceedings, we can help secure court orders preventing criminals from publishing your data, effectively nullifying their ransom demands.
Throughout your incident response, our Digital Forensic and Incident Response specialists maintain continuous coordination. Your dedicated Incident Manager and technical leads deliver regular progress updates, manage risk documentation, and operate within your change control frameworks from initial triage through final recovery.
Our support doesn't end with getting you back on your feet. Once your systems are operational again, Solace Cyber partners with you to strengthen your defences through a threat-based approach. We apply our detailed process framework to build resilient protection for the long term.
8Base operates as a ransomware group focused on financial extortion. Their approach involves publicly exposing victims through name-and-shame tactics, while asserting they specifically target companies that have failed to adequately protect employee and customer data privacy.
8Base typically infiltrates systems through several common vectors:
Protective measures should include:
Following your recovery, Solace Cyber advises revising your business continuity plan to incorporate insights gained from this incident.
Ransomware incidents often result in average losses of about £500,000, whereas smaller email-related breaches tend to cost closer to £50,000. Organisations must decide whether to preserve affected systems for forensic analysis or prioritise rapid recovery to reduce downtime. Any delay in detection or remediation quickly increases financial impact.
Cyber insurance claims involve several layers, including coverage for investigation, remediation, legal expenses, business interruption, liability, and ransom demands. Although insurers provide crucial support for recovery, the cyber insurance market remains unpredictable, with policies often demanding thorough verification.
Expert guidance makes all the difference, this is where Solace Cyber provides clarity and control.
In the face of mounting pressure, your next move is critical. The wrong decision could result in extended downtime, reputational fallout, and the loss of sensitive client information. With limited chances of success, seeking help from an experienced ransomware response team is your safest and most effective option.
Important Reminder: Paying anyone on the financial sanctions list is illegal. This list changes frequently, so it’s vital to confirm the latest status before proceeding.
It’s possible that some of the compromised files include your customers’ personal information. Protecting this type of data is a legal obligation, so you may need to inform those affected.
Your insurer or legal advisor will guide you through the correct process and next actions. Solace Cyber regularly works alongside insurers and legal teams and can help coordinate communication and support during this period.
A cyber breach can interrupt every part of a business, with potential outcomes that reach far beyond the initial incident:
Mitigation depends on a robust incident response plan that covers rapid action, transparent communication, and collaboration with cybersecurity professionals. By focusing on recovery, strengthening resilience, and rebuilding stakeholder confidence, businesses can limit long-term harm and return to full strength faster.
Under Australian law, organisations experiencing ransomware attacks must report incidents to both the Australian Signals Directorate (ASD) and the Office of the Australian Information Commissioner (OAIC), particularly when personal information is compromised, ensuring regulatory compliance and coordinated national response.
Keep calm and step away from your systems.
Avoid restoring files or altering data in any way, as doing so may complicate recovery efforts.
Reach out to Solace Cyber now on +61 (0) 282 786100 or submit our contact form to have an expert return your call.
We’ll take swift action to minimise downtime and restore stability to your operations.

Solace Cyber helps companies across Australia recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 08830710

Solace Cyber
Zensec Ltd,
60 Martin Place,
Sydney,
NSW 2000
Telephone
Please note that calls may be recorded for security and training purposes.