First detected in February 2019, Cl0p is a Russian-language ransomware operation regarded as a serious cyber threat affecting organisations of all types.
A Cl0p attack becomes clear when a ransom notice appears on screen confirming that access to your network has been blocked and your files have been encrypted. The group behind the attack will request a payment, usually via cryptocurrency to maintain anonymity. Refusing to pay can result in threats to destroy your files or publish them online.
If someone broke into your physical premises, you would contact the police immediately and preserve the scene for evidence gathering. Cyber incidents require the same disciplined response.
Your first move is to bring in digital forensics specialists and leave the affected systems untouched. This falls outside the remit of internal IT teams or managed service providers. Dedicated forensic professionals operate around the clock and can take control.
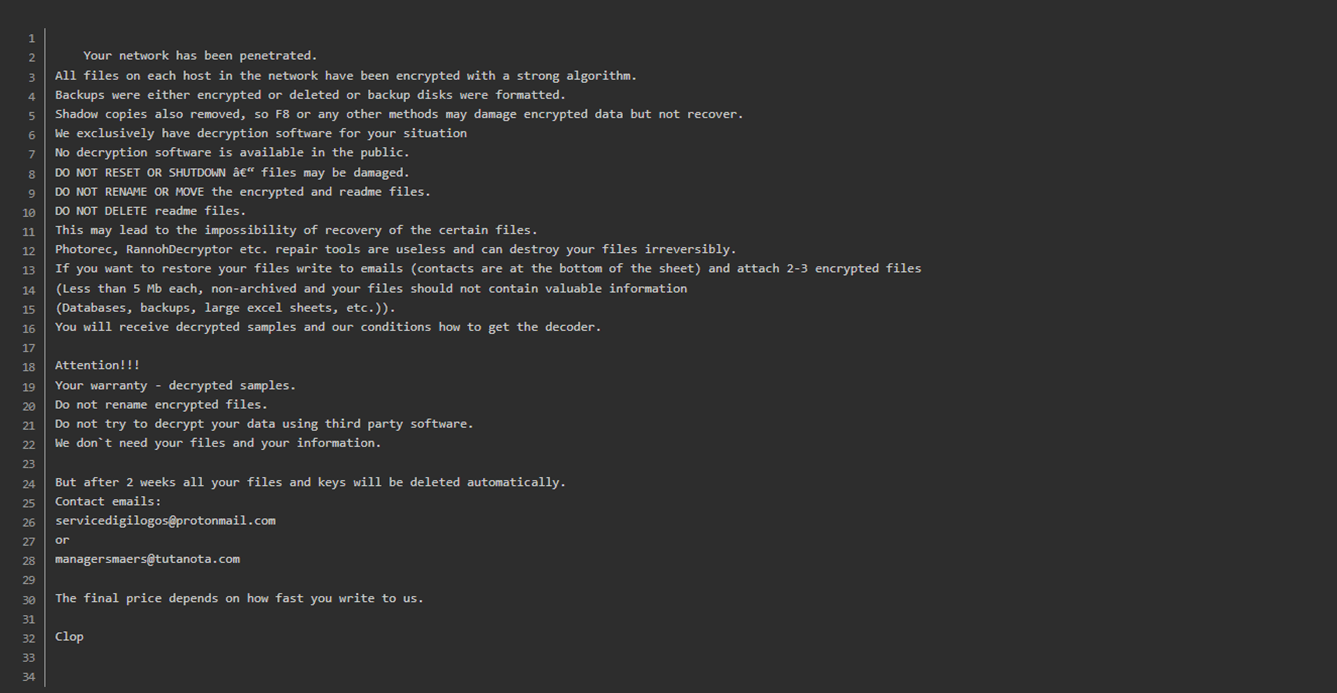
You can confirm a Cl0p intrusion if a message resembling the one shown appears across your devices.
Cl0p is a well-established ransomware operation within Russian-speaking cybercrime networks. The group is financially motivated and closely linked to threat actor TA505. Reports attribute more than $500 million in ransom payments to attacks carried out against major organisations across the globe, making it one of the most damaging groups of its kind.
The group became widely known in 2019 after a series of disruptive incidents. Its campaigns have historically relied on extensive phishing activity and sophisticated malware designed to infiltrate systems, encrypt data and demand payment in exchange for decryption keys. Victims are warned that confidential information will be exposed publicly if they refuse to comply.
Infections are easily identified by the “.clop” extension attached to encrypted files and ransom messages marked with the phrase “Dont Worry C|0P”. The ransomware is derived from the CryptoMix family and includes functionality intended to disable security tools such as Windows Defender and Microsoft Security Essentials to help avoid detection.
Cl0p has recently shifted its approach. Rather than focusing on phishing emails as its primary delivery method, the group now concentrates on exploiting security flaws within public-facing systems to gain initial access and compromise infrastructure.
Cl0p targets organisations through data theft and extortion. Rather than always encrypting files, the group increasingly uses an “encryption-less” approach, stealing information and threatening to publish it if payment is refused. This achieves the same coercive impact while reducing their workload and increasing financial return.
The group applies pressure by contacting external stakeholders or deploying further malware intended to cause operational disruption. Ransom amounts are adjusted according to the organisation’s perceived financial capacity, and payment is usually requested in cryptocurrency to reduce traceability. The threat combines financial loss with reputational consequences to drive victims to comply.
Cl0p appeared in February 2019, meaning it has been active for about five years as of January 2025.
Since then, records show 1,014 confirmed victims.
With round-the-clock availability every day of the year, Solace Cyber has delivered Digital Forensic Incident Response services across hundreds of successful recovery operations in Australia.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
“In 2024, the NCSC issued 542 notifications informing organisations of a cyber incident impacting them, more than double the 258 notifications issued in 2023.”
When a cyber incident occurs, take these immediate actions:
Solace Cyber acts as your specialist digital forensics partner in Australia, helping restore normal operations swiftly. Our response includes:
Recovery timelines typically range from 2 weeks to 2 months, depending on the incident's scope.
Solace Cyber delivers global risk and security services across Australia, specialising in travel, crisis support, and offshore risk management. The organisation runs a fully staffed security operations centre around the clock and maintains an internal intelligence unit that produces routine daily and weekly updates. The business is certified to ISO 27001, ISO 14001, ISO 45001, and ISO 9001 standards.
Founded in the UK in 2021, Solace Cyber has grown its presence throughout Australia, concentrating on cyber incident handling, including digital forensics, incident response, ransomware events, information security, and wider risk management, supported by managed security services. The senior leadership team has more than two decades of combined experience across security and IT.
s
%+
Specialist forensic investigation and secure restoration demand focused expertise that standard IT departments rarely possess. Your internal teams excel at day-to-day technology support, but ransomware response requires dedicated capabilities they typically lack.
Consider these key challenges facing in-house teams:


We created Solace Cyber specifically to address ransomware incidents through our structured 6-phase methodology:
Our comprehensive forensic investigation begins at phase 2, forming the foundation of your business continuity plan. This detailed analysis proves essential for:
We execute our evidence examination according to a carefully structured protocol designed to identify root causes quickly. This discovery directly informs our eradication strategy and recovery plan, while building the evidence base for potential legal action. Through legal proceedings, we can help secure court orders preventing criminals from publishing your data, effectively nullifying their ransom demands.
Throughout your incident response, our Digital Forensic and Incident Response specialists maintain continuous coordination. Your dedicated Incident Manager and technical leads deliver regular progress updates, manage risk documentation, and operate within your change control frameworks from initial triage through final recovery.
At Solace Cyber, our support doesn't end with recovery. After your business is operational again, we partner with you to enhance your cybersecurity. Our comprehensive process is designed to provide a proactive, threat-informed strategy for long-term protection.
Cl0p ransomware is widely attributed to a financially driven, Russian-speaking cybercriminal group operating a ransomware-as-a-service model.
Systems are typically compromised through several common entry points, including:
To strengthen resilience, organisations should prioritise measures such as:
Once operations are restored, Solace Cyber advises reviewing and updating your business continuity plan, integrating any insights gathered throughout the incident and recovery process.
Ransomware attacks can cost businesses around £500K on average, with smaller breaches involving email data typically around £50K. There is often a balancing act between preserving the environment for forensics and recovering quickly to minimise business disruption. The longer it takes to identify and resolve the breach, the higher the costs will be.
Filing a cybersecurity insurance claim is complex and covers investigation, remediation, legal costs, business interruption, criminal liability, employment liability, and ransom payments. However, the cyber insurance market is volatile, and many policies are not properly validated, which can affect recovery efforts.
Criminal groups like Cl0p receive payments from affiliates to launch cyber-attacks using malware known for its rapid encryption capabilities. Even if the ransom is paid, the chances of successfully recovering the data are slim, highlighting the importance of engaging a ransomware incident response team.
Important Note: Paying individuals or organisations subject to financial sanctions is illegal. The list of sanctioned entities is frequently updated.
It is highly likely that some of the data lost during the attack may be classified as “Personal Data” under data protection laws. You are legally required to safeguard this data, but it may have been compromised, so you should consider notifying customers.
Your insurer or legal team will guide you on the best course of action moving forward.
Solace has extensive experience collaborating with insurers and legal professionals and can offer support during this challenging time.
A ransomware attack poses significant risks to your business, including:
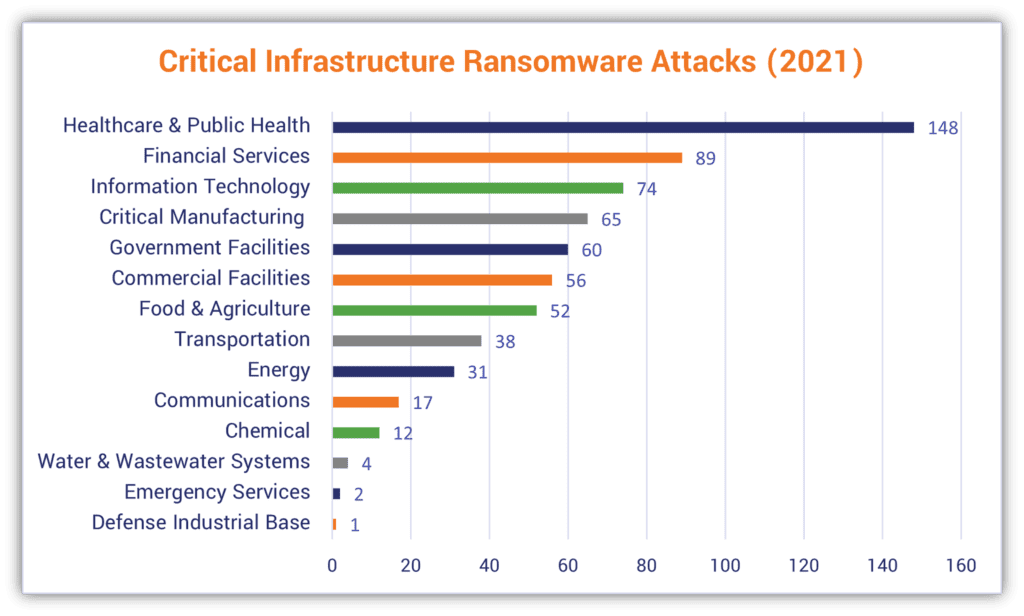
Ransomware is one of the most damaging threats to businesses, second only to the effects of going into receivership.
Under Australian law, organisations experiencing ransomware attacks must report incidents to both the Australian Signals Directorate (ASD) and the Office of the Australian Information Commissioner (OAIC), particularly when personal information is compromised, ensuring regulatory compliance and coordinated national response.
Keep calm and step away from your systems.
Avoid restoring files or altering data in any way, as doing so may complicate recovery efforts.
Reach out to Solace Cyber now on +61 (0) 282 786100 or submit our contact form to have an expert return your call.
We’ll take swift action to minimise downtime and restore stability to your operations.

Solace Cyber helps companies across Australia recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 08830710

Solace Cyber
Zensec Ltd,
60 Martin Place,
Sydney,
NSW 2000
Telephone
Please note that calls may be recorded for security and training purposes.