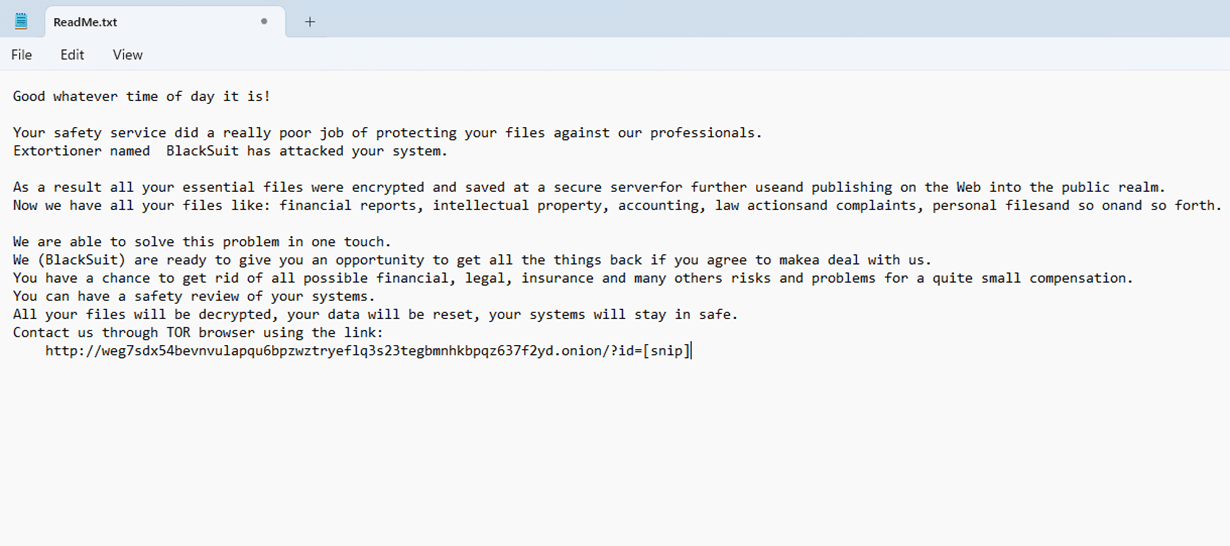
An infection with BlackSuit is characterised by your systems displaying a notice like the one shown here, with the specialist cyber crime group holding your infected systems and stolen data hostage, until you pay a ransom. The ransom is typically demanded in cryptocurrency such as bitcoin.
If you discover a physical break-in at your offices, your first thought would be to call the police; touch nothing and let them search for clues. Then, work out how to get your business operations back up and running.
A cyber-attack requires the same logic. Your environment is a CRIME SCENE. It's imperative for the environment to remain untouched so that a forensic investigation can be carried out. This is not a job for your IT team or MSP. There are Digital Forensic specialists available 24/7 who can assist you, just like in a physical crime.
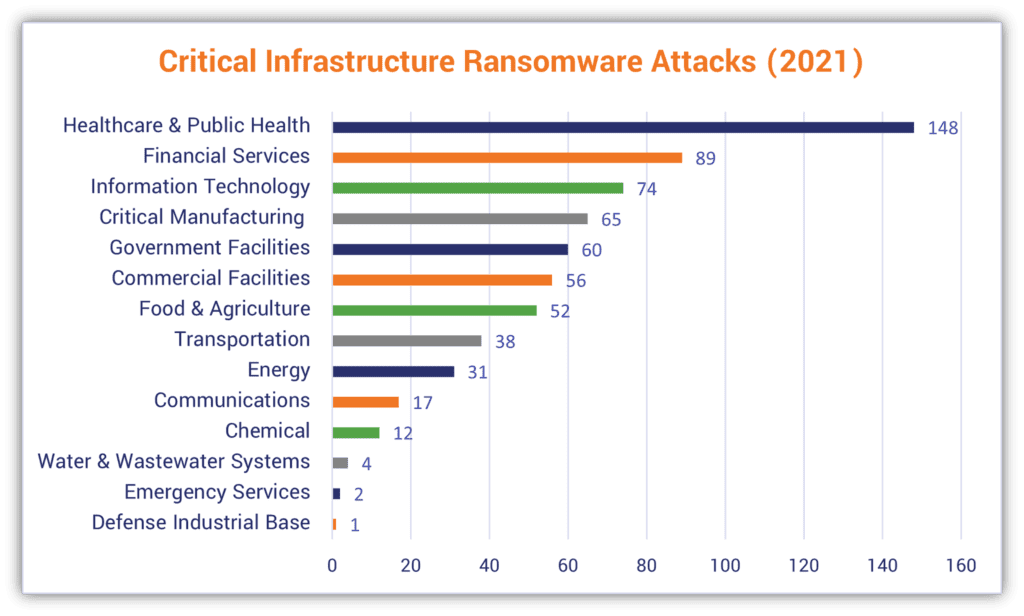
Emerging in April/May 2023, the relatively new ransomware group bears similarities to the Royal ransomware family, which is a direct successor of the defunct Russian-linked Conti operation. With significant attacks targeting organisations in healthcare, education, and other critical industries, BlackSuit has become one of the most active ransomware groups currently operating.
Mainly focusing on Linux and Windows systems, BlackSuit delivers its payloads through phishing emails or third-party frameworks. Additionally, the use of malicious torrent files has been observed as a delivery method for BlackSuit ransomware. BlackSuit then employs double extortion tactics, stealing sensitive data and promptly encrypting the compromised network. As part of this strategy, they set up a data leak site to pressure victims into paying the ransom demand.
BlackSuit employ double extortion tactics which involves encrypting a victim's data making it inaccessible, and then exfiltrating sensitive information, such as personal or company data. The threat actors demand payment for both decrypting the files and preventing the release of the data on the dark web.
This dual threat significantly increases pressure on the victim to pay the ransom, even if they have backups, as the potential data exposure poses serious risks, including reputational damage and legal consequences. This tactic has become increasingly popular among cybercriminals because it maximises their chances of receiving payment.
Emerging in 2023, BlackSuit has shown striking parallels to Royal, the direct successor of the infamous Russian-linked Conti operation, suggesting its origins are older than what we know.
Since mid-2023, the group has claimed 184 victims.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
"As of January 2024, 21% of UK businesses reported experiencing data breaches monthly, with 18% encountering breaches weekly."
Read more...
When a cyber incident occurs, take these immediate actions:
Solace Cyber acts as your specialist digital forensics partner in Australia, helping restore normal operations swiftly. Our response includes:
Recovery timelines typically range from 2 weeks to 2 months, depending on the incident's scope.
Solace Cyber delivers global risk and security services across Australia, specialising in travel, crisis support, and offshore risk management. The organisation runs a fully staffed security operations centre around the clock and maintains an internal intelligence unit that produces routine daily and weekly updates. The business is certified to ISO 27001, ISO 14001, ISO 45001, and ISO 9001 standards.
Founded in the UK in 2021, Solace Cyber has grown its presence throughout Australia, concentrating on cyber incident handling, including digital forensics, incident response, ransomware events, information security, and wider risk management, supported by managed security services. The senior leadership team has more than two decades of combined experience across security and IT.
s
%+
A forensic analysis needs to be meticulous and a clean restore and recovery requires a wealth of experience not normally available in an in-house team who must provide a broader range of IT support skills:


Solace Cyber was established precisely for this scenario. We have a well-defined process for handling cyber-attacks like BlackSuit, which involves a 6-step approach:
It includes a thorough digital forensic analysis from step 2 where the output becomes a central component of business recovery. This is because understanding the attack is of critical importance:
It is critical that the analysis of digital evidence is carried out to an agreed plan. This will have been designed to provide the best and earliest chance of discovering a root cause, which is essential to inform remediation/eradication and recovery as well as supporting a legal take-down case if this is applicable. A legal take-down means we can assist in the legal enforcement that stops the criminals from publishing the data, thus undermining the ransom notice.
Solace’s Digital Forensic and Incident Response teams maintain consistent communication throughout. Dedicated Incident Managers and technical engineering leads provide updates during the Cyber Incident Response journey, utilising risk registers and working within change management processes, all from triage through to post-incident, delivering successful business recovery.
Solace Cybers’ support continues beyond the recovery process. Once your business is back up and running, we work with you to transform your cyber security through a threat-informed approach utilising our 9-step approach Solace Global - Cyber 9 Step Process.
The BlackSuit ransomware entered your system by one of several ways:
We recommend you adopt policies to:
After recovering from BlackSuit, Solace Cyber recommends that you update your business continuity plan to account for lessons learnt during this attack & recovery.
Most ransomware breaches cost approx £500K with smaller email data breaches in the realm of £50K. There is a dichotomy of preserving the environment for forensics or recovering it quickly for less business interruption. The cost increases the longer it takes to identify the breach and resolve it.
A Cyber Security insurance claim is complex and includes reasonable expenses to investigate and remediate an incident along with cover for legal, business interruption, criminal liability, employment liability and ransom policies. The insurance industry is liable to deliver the business recovery BUT Cyber insurance is viewed as volatile within the industry and many insurance policies are not being validated correctly.
Navigating through this requires experience, which is where Solace Cyber can help.
Criminal organisations like BlackSuit are paid by affiliates to launch cyber-attacks using their specific brand of malware that is known for its swift and efficient encryption capabilities. Even if the ransom is paid, the likelihood of having files decrypted and data restored is minimal, underscoring the necessity of employing a ransomware incident response team.
The NCSC have documented the deliberations for paying ransomware: https://www.ncsc.gov.uk/ransomware/home
Important Reminder: It is a criminal offense to pay money to people who are subject to financial sanctions. The list of who is subject to financial sanctions is constantly changing.
The latest iteration can be found here: https://www.gov.uk/government/publications/financial-sanctions-consolidated-list-of-targets
Almost certainly, yes. It is possible that some of the data lost is classified as “Personal Data” to your customer. You have a legal obligation to protect that data but it may have been lost. You may also need to advise the Information Commissioner's Office (ICO) at https://ico.org.uk/.
Your insurer/legal council will advise you on what to do and how to proceed with this.
Solace has experience working with insurers and lawyers and can help in this relationship at this stressful time.
A ransomware attack poses the biggest threat to your business by:
If you have a business interruption, how do you know where you are in your supply chain for any one item and how do you carry on with your business? If it persists for a long time, how do you maintain your operation? And when your systems and data are restored, how do you backfill with any work you did and how do you operate going forward?
Ransomware is second only to receivership for debilitating a business.
Action Fraud is the UK’s national reporting centre for fraud and cybercrime. Whether you have been scammed, defrauded, or experienced cybercrime in England, Wales, or Northern Ireland, Action Fraud offers a central point of contact for information on fraud and financially motivated cybercrime.
If your systems are showing signs of a BlackSuit attack, REMAIN CALM.
YOU MUST NOT TOUCH THEM, RESTORE OR OVERWRITE THE DATA (explanation above).
Contact Solace Cyber on +61 (0) 282 786100 or complete our form for a call back from one of our experts.
We will act promptly to reduce your business downtime.

Solace Cyber helps companies across Australia recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 08830710

Solace Cyber
Zensec Ltd,
60 Martin Place,
Sydney,
NSW 2000
Telephone
Please note that calls may be recorded for security and training purposes.