Akira, a Russian ransomware collective, surfaced in March 2023 and has rapidly risen to prominence as a major cyber threat.
Signs of an Akira attack typically include a system-wide alert indicating that files are locked and inaccessible. Once the encryption is complete, the attackers issue a ransom demand, most often requesting cryptocurrency to conceal the transaction. If payment isn’t made, victims are often warned that their data will be deleted or publicly released.
If you arrived at work to discover a physical break-in, your instinct would be to call the police and avoid disturbing the scene to preserve evidence.
A ransomware attack should be treated with the same caution. The system must remain untouched so that a full forensic investigation can be carried out by qualified Digital Forensics experts. This process falls outside the remit of your internal IT team or managed service provider.
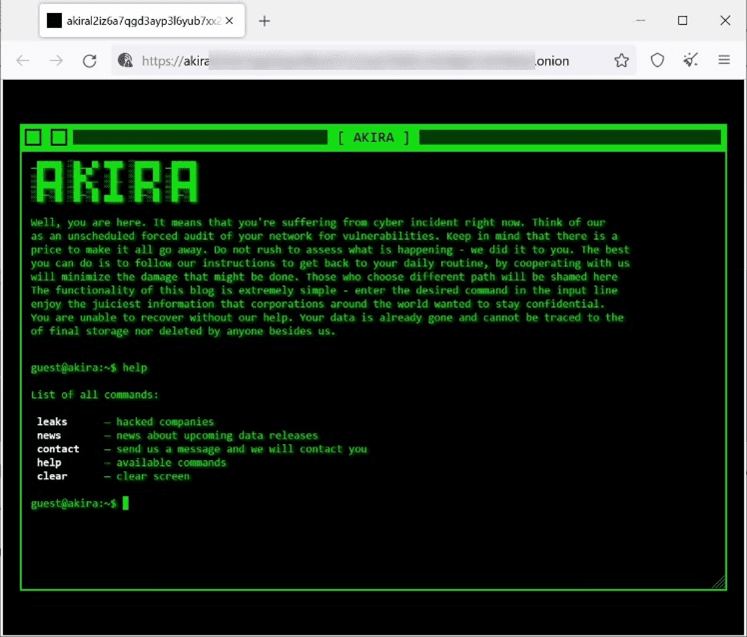
If your screen displays a ransom message similar to the one above, it’s a strong indicator that you’ve been targeted by an Akira Ransomware attack.
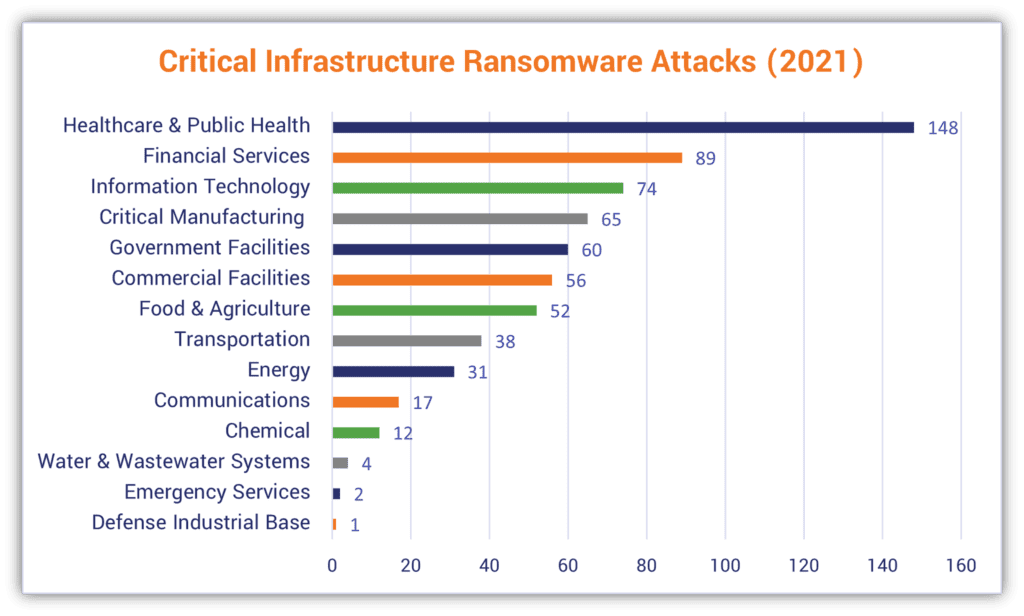
Akira is a Russian ransomware collective that surfaced in March 2023. Since then, it has launched widespread attacks against organisations across multiple sectors, including education, finance, manufacturing, and vital infrastructure. The group’s main focus has been on small and medium-sized businesses in the US, Europe, and Canada, earning it a reputation as one of the fastest-expanding cybercrime operations in recent years. The group’s ransom notes are distinctive, featuring a retro design inspired by the 1988 Japanese anime film Akira.
Akira gains access by exploiting vulnerabilities in public-facing systems such as web servers, databases, and business applications. They have also been known to breach networks through flaws in VPNs and weaknesses in multi-factor authentication. Operating under a Ransomware-as-a-Service (RaaS) model, Akira uses multi-extortion tactics, stealing data before encrypting it, then pressuring victims to pay through a TOR-based negotiation site where the stolen data is hosted.
If you encounter a ransom note resembling this description, your system has likely been compromised by Akira ransomware. Do not interfere with or attempt to restore the affected files. The system must remain untouched so that digital forensic specialists can conduct a proper investigation. This should never be handled by internal IT teams or managed service providers.
Akira uses a double-extortion strategy, encrypting a target’s files to block access while also stealing confidential data, including personal and corporate information. The attackers then demand payment both to decrypt the files and to stop the stolen data being released on the dark web.
This two-pronged method puts added pressure on victims to comply, even when secure backups exist, as the threat of data exposure can lead to serious reputational harm and possible legal action. The approach has become increasingly common among cybercriminal groups because it raises the likelihood of a successful ransom payout.
Akira is a relatively recent ransomware operation, first identified in 2023, and it is believed to have operational ties to the now-defunct Conti ransomware group.
Since its emergence, Akira has been linked to more than 900 confirmed attacks worldwide.
With round-the-clock availability every day of the year, Solace Cyber has delivered Digital Forensic Incident Response services across hundreds of successful recovery operations in Australia.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
“The number of active ransomware groups more than doubled year-over-year, increasing 55% from 29 distinct groups in Q1 2023 to 45 distinct groups in Q1 2024.”
When a cyber incident occurs, take these immediate actions:
Solace Cyber acts as your specialist digital forensics partner in Australia, helping restore normal operations swiftly. Our response includes:
Recovery timelines typically range from 2 weeks to 2 months, depending on the incident's scope.
Solace Cyber delivers global risk and security services across Australia, specialising in travel, crisis support, and offshore risk management. The organisation runs a fully staffed security operations centre around the clock and maintains an internal intelligence unit that produces routine daily and weekly updates. The business is certified to ISO 27001, ISO 14001, ISO 45001, and ISO 9001 standards.
Founded in the UK in 2021, Solace Cyber has grown its presence throughout Australia, concentrating on cyber incident handling, including digital forensics, incident response, ransomware events, information security, and wider risk management, supported by managed security services. The senior leadership team has more than two decades of combined experience across security and IT.
s
%+
Specialist forensic investigation and secure restoration demand focused expertise that standard IT departments rarely possess. Your internal teams excel at day-to-day technology support, but ransomware response requires dedicated capabilities they typically lack.
Consider these key challenges facing in-house teams:


We created Solace Cyber specifically to address ransomware incidents through our structured 6-phase methodology:
Our comprehensive forensic investigation begins at phase 2, forming the foundation of your business continuity plan. This detailed analysis proves essential for:
We execute our evidence examination according to a carefully structured protocol designed to identify root causes quickly. This discovery directly informs our eradication strategy and recovery plan, while building the evidence base for potential legal action. Through legal proceedings, we can help secure court orders preventing criminals from publishing your data, effectively nullifying their ransom demands.
Throughout your incident response, our Digital Forensic and Incident Response specialists maintain continuous coordination. Your dedicated Incident Manager and technical leads deliver regular progress updates, manage risk documentation, and operate within your change control frameworks from initial triage through final recovery.
Solace Cyber’s commitment doesn’t end once your systems are restored. After recovery, our team partners with you to reinforce your defences using a threat-led strategy built around our comprehensive process.
Akira does indeed use a Ransomware-as-a-Service approach, making their ransomware variant available to affiliate distributors.
The attack succeeded through three primary methods:
Essential Security Measures Moving Forward:
To strengthen your defences, implement these critical policies:
Following your recovery from this Akira ransomware incident, Solace Cyber advises revising your business continuity plan to incorporate the insights gained throughout the attack and recovery process.
Typical ransomware incidents result in financial losses around £500,000, while smaller email-related data breaches generally cost approximately £50,000. Organisations face a critical decision: maintain the digital environment intact for forensic investigation or prioritise swift system restoration to minimise operational disruption. Extended detection and resolution periods compound these costs significantly.
Filing a cybersecurity insurance claim involves considerable complexity, encompassing justifiable expenditure for incident investigation and remediation, alongside provisions for legal costs, operational downtime, criminal exposure, workforce-related liabilities and ransom payment coverage. Insurance providers bear responsibility for facilitating business continuity following an incident. However, the cyber insurance sector faces considerable uncertainty, with numerous policies failing to undergo proper validation procedures.
Successfully managing these challenges demands specialist knowledge. Solace Cyber provides the expertise needed to guide you through this process.
Law enforcement strongly advises against paying ransom demands. Even if you decide to pay, there's no assurance you'll regain access to your data or stop it from being distributed on the dark web. A growing trend has seen ransomware affiliates profit from stolen data beyond the scope of their original Ransomware-as-a-Service (RaaS) agreements.
Key Reminder: Paying individuals or entities subject to financial sanctions is a criminal offence. Keep in mind, the list of those under financial sanctions is regularly updated.
It’s highly probable. The lost data could be considered "Personal Data" under data protection laws, which means you are legally required to safeguard it. Given that a ransom attack may have compromised this data, you have both a legal and ethical obligation to notify your customers.
Fortunately, your insurer or legal advisor can provide guidance on the appropriate actions to take. Alternatively, Solace has extensive experience working alongside insurers and legal teams and can assist in managing these relationships during this difficult time.
A ransomware attack represents one of the greatest risks to your business by:
For this reason, ransomware is considered one of the most damaging threats to a business, second only to receivership.
Under Australian law, organisations experiencing ransomware attacks must report incidents to both the Australian Signals Directorate (ASD) and the Office of the Australian Information Commissioner (OAIC), particularly when personal information is compromised, ensuring regulatory compliance and coordinated national response.
Keep calm and step away from your systems.
Avoid restoring files or altering data in any way, as doing so may complicate recovery efforts.
Reach out to Solace Cyber now on +61 (0) 282 786100 or submit our contact form to have an expert return your call.
We’ll take swift action to minimise downtime and restore stability to your operations.

Solace Cyber helps companies across Australia recover from ransomware attacks and data breaches.
Ransomware Recovery
Ransomware Groups
BEC Recovery
About Us
Blog
News
SOLACE CYBER LTD is registered in England & Wales no. 08830710

Solace Cyber
Zensec Ltd,
60 Martin Place,
Sydney,
NSW 2000
Telephone
Please note that calls may be recorded for security and training purposes.